![]()
RangeForce
Cybersecurity Skills Development
Why thinktech?
![]() We are the official and authorized RangeForce training partner in Australia and the wider APAC region
We are the official and authorized RangeForce training partner in Australia and the wider APAC region
![]() We are a dedicated training organization, specializing in technical disciplines and providing training courses in the areas of engineering, networking, Smart Buildings, IoT, digitalization, automation, cybersecurity and related subjects
We are a dedicated training organization, specializing in technical disciplines and providing training courses in the areas of engineering, networking, Smart Buildings, IoT, digitalization, automation, cybersecurity and related subjects
![]() We are serving educational, commercial, IT, data centre, retail, financial industries among others
We are serving educational, commercial, IT, data centre, retail, financial industries among others
![]() Our team is available to provide local and tailored customer support
Our team is available to provide local and tailored customer support
![]() We offer attractive pricing and corporate discounts
We offer attractive pricing and corporate discounts
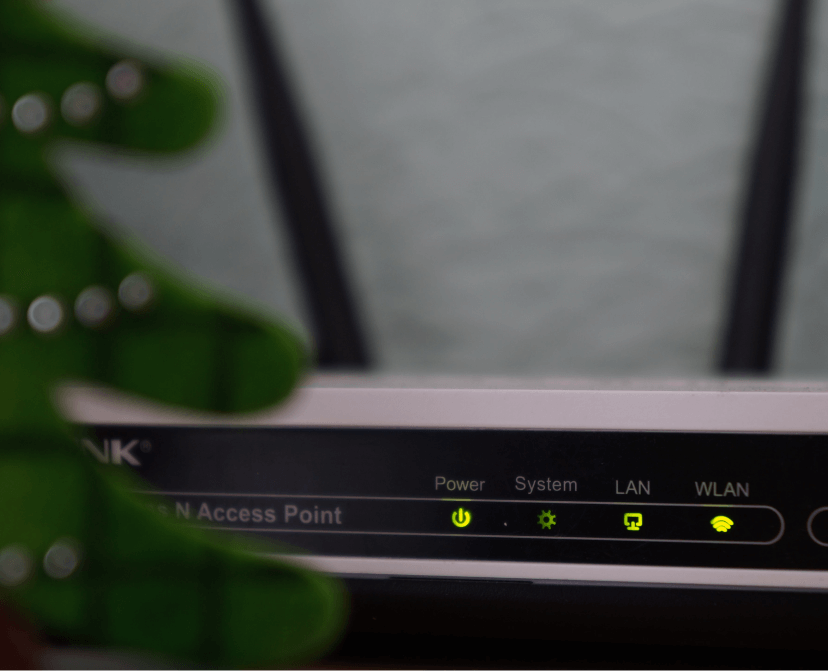
Upskill your team continuously
Ensure defensive readiness across your entire team with realistic and hands-on skills development.
Access hands-on cybersecurity skills training for your entire team.
RangeForce’s library of interactive cybersecurity skill content lives in an emulated, cloud-based environment. The platform can be accessed anywhere, at anytime, enabling safe and scalable learning across your team.
Put real tools and concepts into practice while building the skills needed to defend against the latest threats.
RangeForce Platform Features

Realistic Simulation
RangeForce emulates realistic IT environments. Your team’s training features real security tools, real infrastructure, and real threats.

Guided Learning
A virtual teaching assistant is embedded in the platform interface to guide you and your team through each module, providing helpful hints as needed.

Targeted Skills
Set goals and objectives for your team. Create custom learning plans that align to your organization’s needs.

Reporting and Insights
RangeForce delivers a single point of visibility to track your team’s strengths and weaknesses.

Gamification
Add competition and gamification to your team learning experience with in-platform rewards and leaderboards.

On-Demand Access
RangeForce can be accessed anywhere, at any time. Your team’s training journey is entirely self-paced.
Experience realistic, hands-on training that tests your ability to identify and respond to the latest cyber threats.
RangeForce Learning Paths
RangeForce Learning Paths align with the specific needs of core cybersecurity functions.
Each path features realistic exercises and related challenges.
SOC Analyst 1
The SOC Analyst 1 path enables cybersecurity professionals and students to gain live environment experience with the foundational concepts and practices of a security operations center (SOC). Whether it’s understanding event logs, visualizing data, or conducting malware analysis, this curriculum is designed to get you SOC-ready. Work through a series of hands-on modules and related challenges to complete this path.
SOC Analyst 2
Web Application Security (OWASP)
Threat Hunter
Microsoft Core Security
Cybersecurity Essentials
Secure Coding
RangeForce Training RangeForce training is developed by a global team of cybersecurity experts. We develop defensive and offensive security content continuously, and release new modules weekly.
Training covers the full spectrum of cybersecurity experience levels, from beginner to advanced, for a variety of roles including security operations (SOC), DevSecOps, WebAppSec, PenTesting, and more.

Success Stories

See how the RangeForce simulated training platform helped Barclays:
![]() Improve security culture, coordination, and cooperation across global teams.
Improve security culture, coordination, and cooperation across global teams.
![]() Increase the rectification of security flaws at speed.
Increase the rectification of security flaws at speed.
![]() Continuously upgrade the cyber skill of individuals in a measurable way.
Continuously upgrade the cyber skill of individuals in a measurable way.
See how the RangeForce simulated training platform helped Pipedrive:
![]() Cut training costs by 40%.
Cut training costs by 40%.
![]() Increase self-reported cyber-incident detection by 30%.
Increase self-reported cyber-incident detection by 30%.
![]() Identify new security talent inside the company eliminating expensive hiring needs.
Identify new security talent inside the company eliminating expensive hiring needs.
![]() Evolve their security culture and prepare teams to defend against more sophisticated attacks.
Evolve their security culture and prepare teams to defend against more sophisticated attacks.
See how the RangeForce simulated training platform helped Tallinn University of Technology:
![]() Decrease the preparation and evaluation time of lessons by 90%.
Decrease the preparation and evaluation time of lessons by 90%.
![]() Deliver real-world, hands-on cyberattack simulations turning student into real cyber defenders.
Deliver real-world, hands-on cyberattack simulations turning student into real cyber defenders.
![]() Increase the scale and scope of course work while also increasing the number of students enrolled.
Increase the scale and scope of course work while also increasing the number of students enrolled.

Commercial partnerships and technology tools